Facephi IDV: Your entire identity verification, orchestrated in one console
Deploy faster, manage smarter, and stay compliant across every channel.
Facephi IDV unifies onboarding, authentication, and fraud prevention on a single platform.

About Facephi
Trusted by financial institutions across 30+ countries
Facephi protects digital identity and empowers trust for leading financial institutions, fintechs, and different providers worldwide. Through biometrics, liveness detection, and intelligent orchestration, we secure every stage of the user journey—reducing fraud, ensuring compliance, and improving user experience at scale.
They trust us
Get your identity verification live in weeks, not quarters
Facephi IDV unifies all our identity stack in one console. Configure flows, manage operations, detect fraud, and monitor performance without complex integrations or developer dependencies.
Why teams choose Facephi IDV
-
Fast deployment: Build and launch flows in weeks using visual tools and low-code orchestration.
-
Operational visibility: Centralized dashboards, search, and KPIs across every tenant.
-
Built-in antifraud: Face and device blocklists, audit logs, and traceable decisions.
-
Compliance-ready: One-click audit PDFs and full activity logs for internal or external reviews. Coming soon in 2026
-
Scalable security: Secure onboarding, 1:1 authentication, and continuous verification; all in one environment.
The Building Blocks of IDV
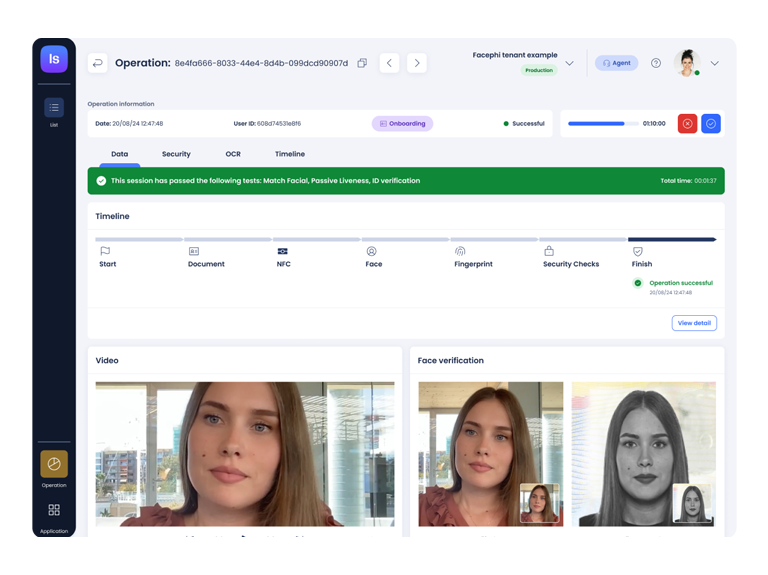
Every verification decision, visible and auditable
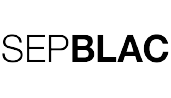
Operations
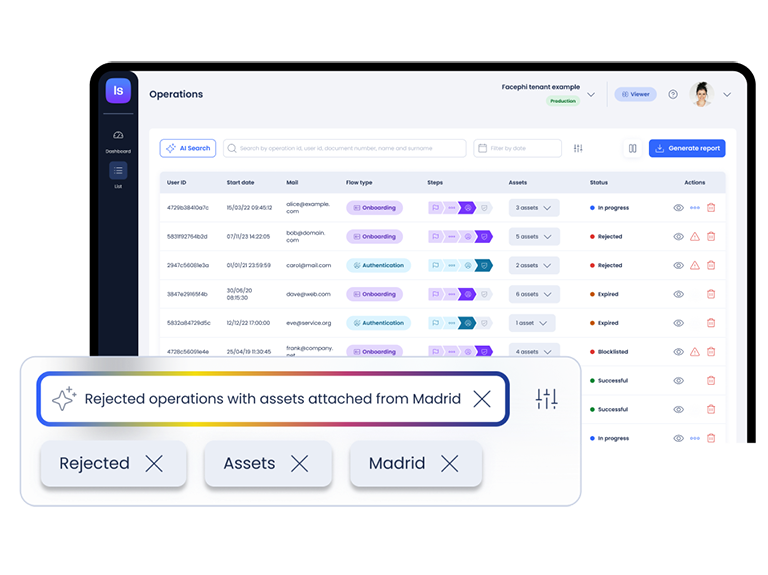
Gain a complete operational view of every verification. See all onboarding and authentication cases in one place, organized by type, status, or platform.
-
Use filters to narrow results by time frame or operation type and immediately update dashboards without page reloads.
-
Use search to locate any operation by user ID, document number, or operation ID with encrypted-field security.
-
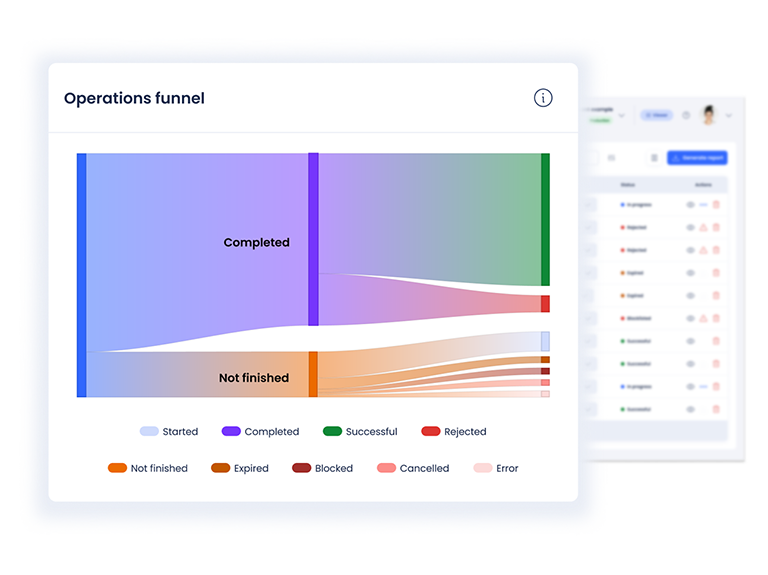
Analyze performance through real-time KPIs: initiated, successful, rejected, and blocked operations.
-
Visualize conversion funnels to detect drop-offs and identify friction points. Access every operation’s assets — biometric captures, documents, and OCR data — directly from the same view.
-
Export audit-ready PDF reports with one click, including all evidences and process details for compliance teams. Coming soon in 2026
Flows & Integrations
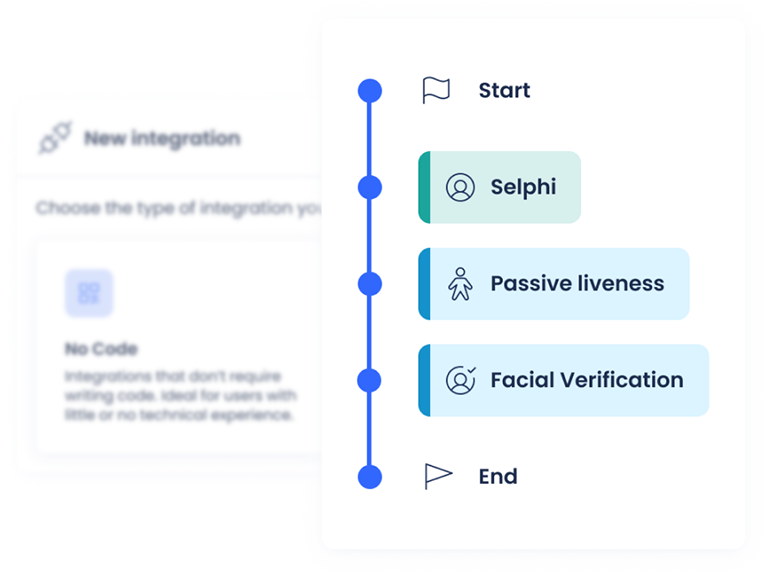
Design and deploy verification flows tailored to your business.
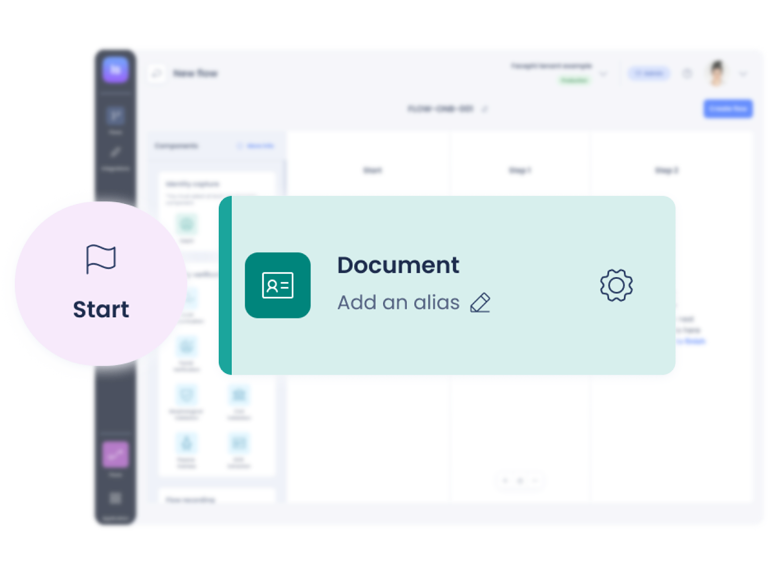
Create and edit onboarding or authentication journeys using pre-built templates as a starting point. Define each step (document capture, selfie, consent, or validation) and set the logic that connects them, ensuring every process meets your security and UX standards.
-
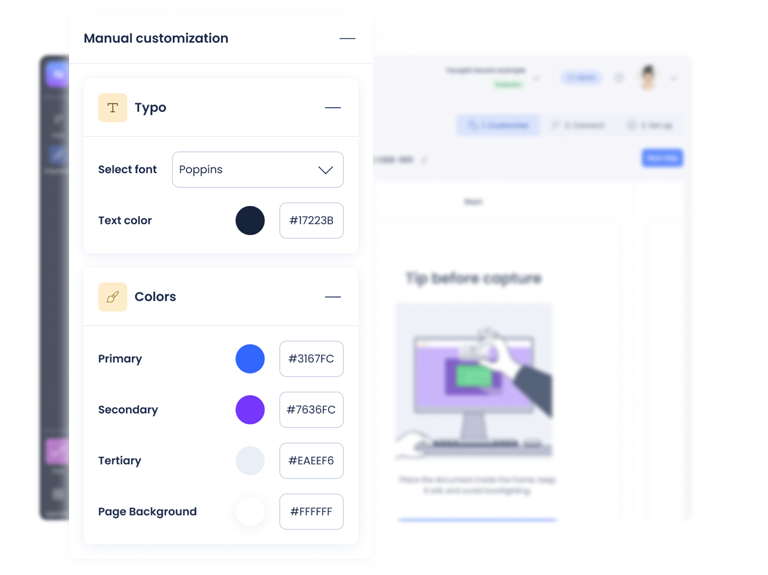
Configure steps and validations visually, without code. Add, remove, or reorder actions, preview the user flow, and make adjustments in real time before publishing.
-
Adapt flows for web or mobile by choosing the environment at setup.
-
Customize the widgets, texts, and validations per channel to guarantee a consistent experience across devices while meeting each client’s branding or technical requirements.
-
Manage integrations to external systems, define API callbacks, and monitor responses.
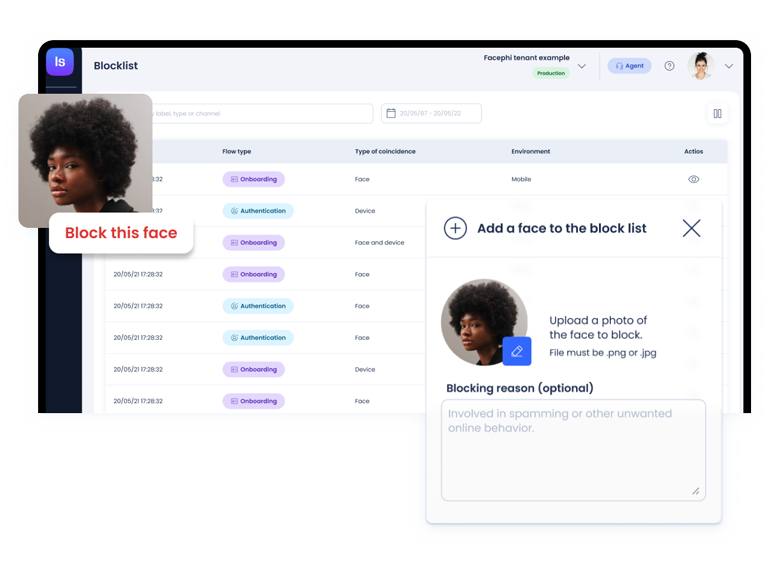
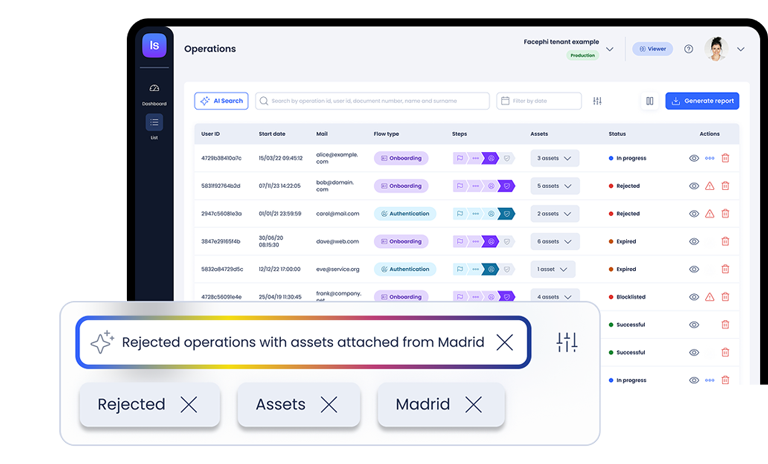
Antifraud
Proactively block identity misuse.
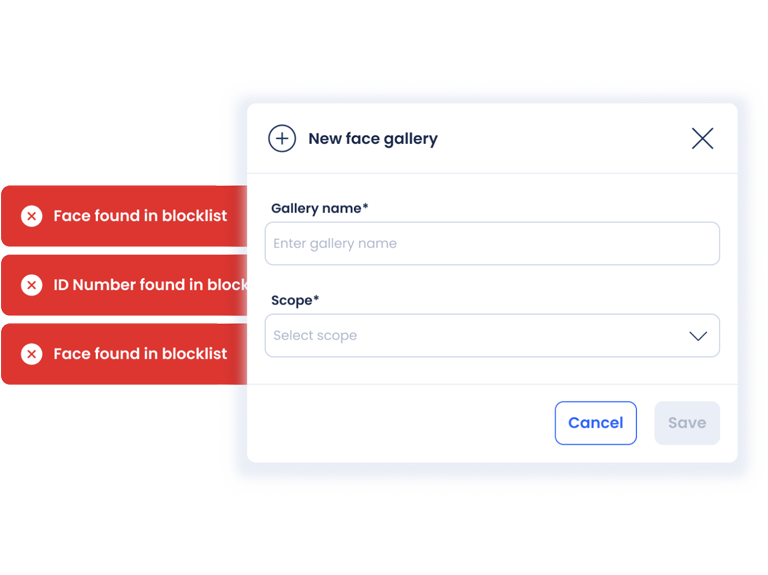
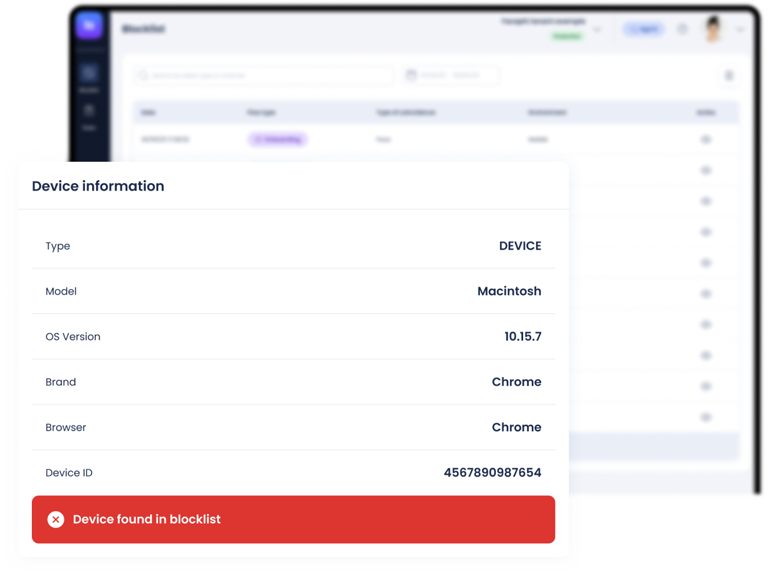
Detect and prevent fraudulent behaviour by comparing every new verification against registered records of faces, devices, or ID numbers previously associated with suspicious activity. The system performs automatic matching between biometric data and stored references, identifying repeated attempts or high-risk patterns before they impact operations.
-
Faces, devices, or identifiers can be added to blocklists manually from the operation detail or automatically.
-
Blocklists can function locally within a tenant or synchronize with shared galleries at regional or global level.
-
Audit-ready reports can be generated at any time, listing all blocked operations filtered by type, period, or reason to support fraud analysis and regulatory review. Coming soon in 2026
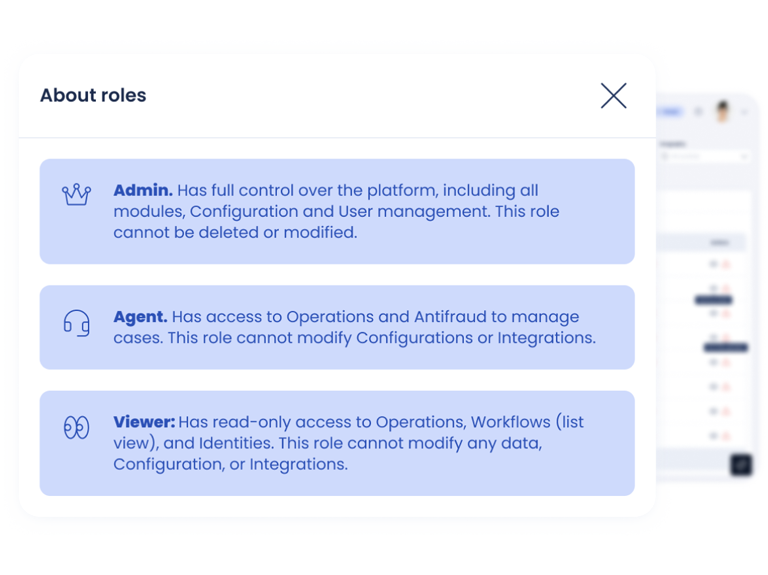
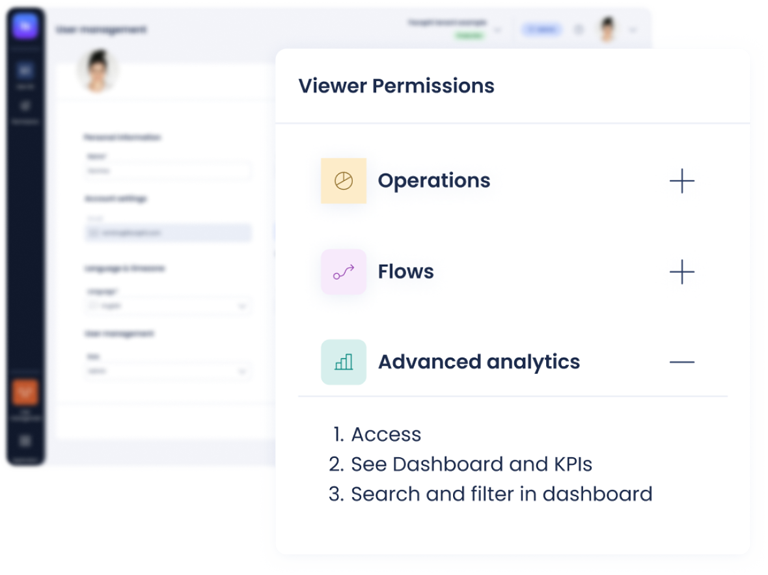
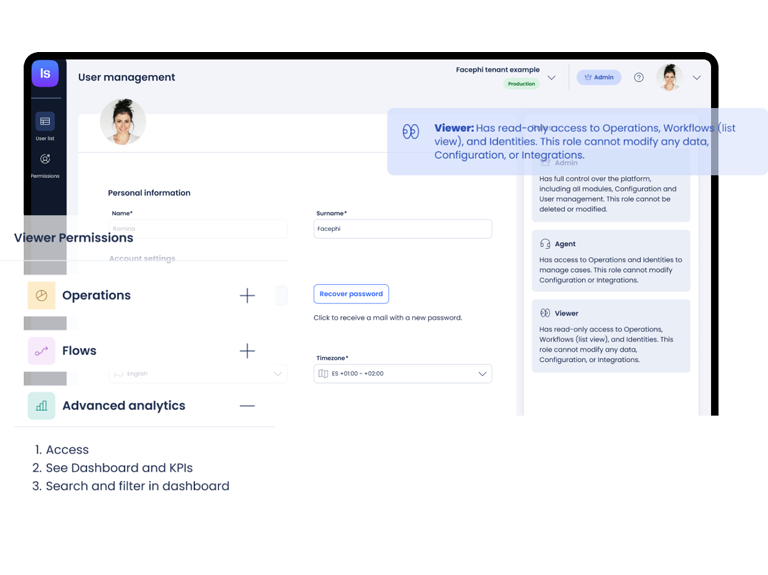
User management
This module enables the creation, editing, and removal of users within each tenant, with role-based permissions that define which modules and actions are available to every profile (Administrator, Agent, or Viewer).
-
Access rights are governed through a detailed role-permission model.
-
All relevant user actions are automatically recorded in the audit log
-
Integration with Active Directory and Azure environments.